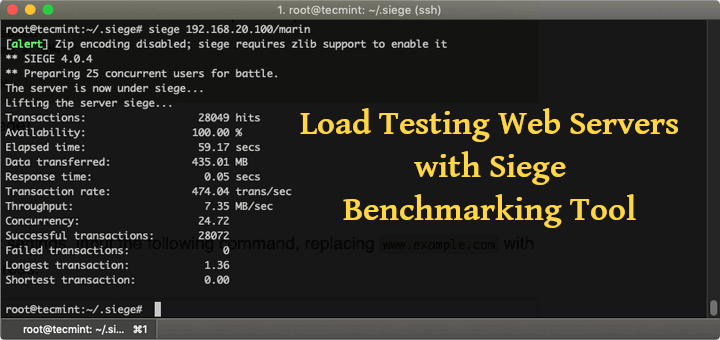
Knowing how much traffic your web server can handle when under stress is essential for planning future grow of your website or application. By using tool called siege, you can run a load test on your server and see how your system performs under different circumstances.
You can use siege to evaluate the amount of data transferred, response time, transaction rate, throughput, concurrency and how many times the server returned responses. The tool has three modes, in which it can operate – regression, internet simulation and brute force.
Important: Siege should only be ran against servers you own or on such you have explicit permission to test. In some countries, using siege on unauthorized websites can be considered a crime.
Installing Siege HTTP Load Testing Utility in Linux
Siege is multi platform and can be installed under Ubuntu/Debian and CentOS/RHEL distributions using following commands.
To install Siege under Debin/Ubuntu, you can run:
$ sudo apt install siege
For CentOS/RHEL, you need to install and enable repository to install siege with:
# yum install epel-release # yum install siege
Alternatively, you can build the Siege from source. For that purpose you will need to have build-essential and development packages installed.
$ sudo apt install build-essential #Ubuntu/Debian # yum groupinstall 'Development Tools' #CentOS/RHEL
Then you can download Siege using wget command and install from sources as shown.
$ wget http://download.joedog.org/siege/siege-latest.tar.gz $ tar -zxvf siege-latest.tar.gz $ cd siege-*/ $ sudo ./configure --prefix=/usr/local --with-ssl=/usr/bin/openssl $ sudo make && make install
Configuring Siege HTTP Load Testing Utility in Linux
Once you have completed the installation, you can adjust your siege configuration file. It is located in /etc/siege/siegerc. In case you have decided to build the package from source, you will have to run:
$ sudo siege.config
This will generate siege.conf file located in your user’s home ~/.siege/siege.conf.
The contents of the file should look something like this. Note that I have uncomment the logfile and time directives:
# cat siegerc |egrep -v "^$|#"
Sample Output
logfile = $(HOME)/var/log/siege.log verbose = false color = on quiet = false show-logfile = true logging = false gmethod = HEAD parser = true nofollow = ad.doubleclick.net nofollow = pagead2.googlesyndication.com nofollow = ads.pubsqrd.com nofollow = ib.adnxs.com limit = 255 protocol = HTTP/1.1 chunked = true cache = false connection = close concurrent = 25 time = 1M delay = 0.0 internet = false benchmark = false accept-encoding = gzip, deflate url-escaping = true unique = true
With the current configuration, siege will imitate 25 concurrent users over 1 minute.
You are now ready to run your siege.
Testing Website Load with Siege Benchmarking Utility
Running siege is quite easy, you only need to specify the website you wish to test like this:
# siege example.com
If the availability remains at 100% and there are no failed connections, your system did well and there were no issues. You should also keep an eye on the response time.
Run Siege Against Multiple Websites
You can test multiple URLs, by setting siege to read them from the file. You can describe the URLs in /usr/local/etc/urls.txt
Now to tell siege to test the URLs from the file, use the -f option like this:
# siege -f /usr/local/etc/urls.txt
You can also use command-line options if you want to try different settings from the ones described in the configuration file.
-C– specify your own configuration file.-q– suppresses siege’s output.-g– GET, pull down HTTP headers and display the transaction. Useful for debugging.-c– the number of concurrent users, default is 10.-r– how many times to run the test.-t– how much time to run the test. You can specify S, M, or H ex: –time=10S for 10 seconds.-d– random delay before each request.-b– no delays between requests.-i– user simulation. Uses to hit random URLs.-f– test URLs from specified file.-l– log file.-H– Add a header to request.-A– specify a user agent.-T– Sets Content-Type in request.--no-parser– NO PARSER, turn off the HTML page parser.--no-follow– do not follow HTTP redirects.